Most people skip the security chapter of the OpenClaw course.
That's a mistake.
Microsoft issued a specific warning about running self-hosted AI agents.
Here's what the course actually teaches — and what you need to lock down before you run a single automation.
Why The OpenClaw Course Starts With Security
OpenClaw is powerful.
That's the point.
Browser control.
File system access.
API calls.
Cron jobs.
Mobile notifications.
Every one of those is an attack surface.
A malicious skill could:
- Read your files
- Exfiltrate secrets
- Rack up API costs
- Push bad code to your repo
- Send emails from your account
The OpenClaw course doesn't hide from this.
It addresses it head-on.
Rule #1 — Always Check skill.md Files
Skills are plugins.
OpenClaw has 5,700+ plugins and 2,868 community skills in the Awesome OpenClaw Skills repo.
Not all of them are safe.
The course's rule:
Before installing any skill:
- Read the skill.md file yourself.
- Run it through Claude to audit.
- Rewrite a secure version if anything's sketchy.
Don't skip this.
A single dodgy skill can compromise your whole agent.
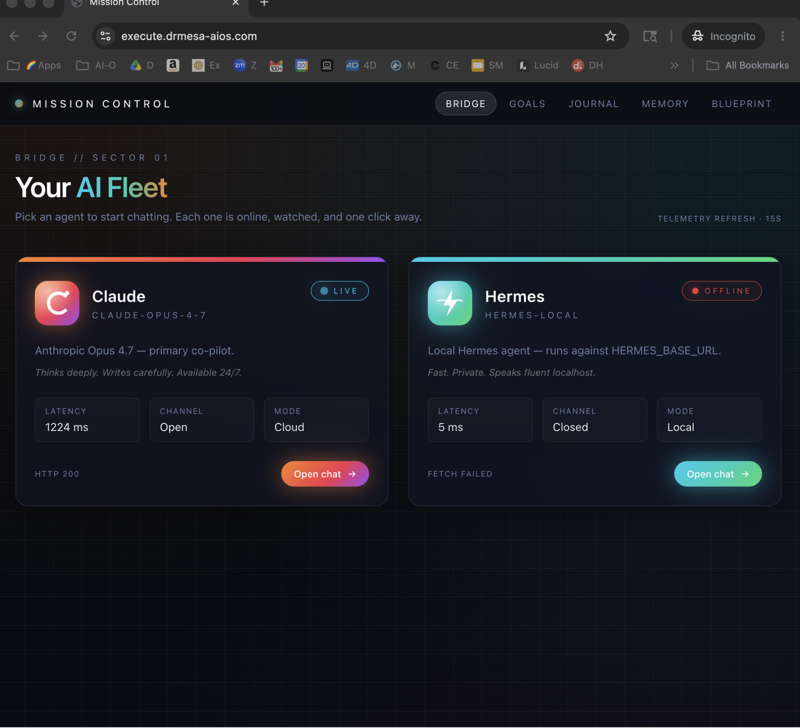
Rule #2 — Run OpenClaw in an Isolated Environment
Microsoft's warning, quoted in the course:
Run OpenClaw in isolated environments — VM, Docker, or Molt Worker via Cloudflare.
Three options.
Virtual machine — simplest. Run OpenClaw in a VM. If something goes wrong, snapshot and restore. Agent can't touch your host files.
Docker — more efficient. OpenClaw has native Docker and Kubernetes support now. Container isolation. Easy to reset.
Molt Worker via Cloudflare — the serverless option. Runs OpenClaw in an ephemeral worker environment. Killed and respawned regularly.
Pick one.
Never run untrusted skills on your main machine.
Rule #3 — External Secrets Management
The course covers the new skills features:
- External secrets management
- Thread-bound agents
- Websocket transport for codex
- Agent routing CLI
- 11+ security fixes
External secrets means your API keys don't sit in a config file.
They live in a secrets manager.
Agents pull them at runtime, in-memory only.
No logs.
No writes.
No leaks.
If a skill tries to exfiltrate — the secrets aren't there to steal.
Rule #4 — Lock Down What the Agent Can Do
Key security updates from the course:
Agent can't rewrite own config — stops self-modification attacks.
SSRF guard — stops agents from poking internal networks (localhost, private IPs).
Workspace ENV injection blocked — agents can't set environment variables to manipulate shell behaviour.
Device pairing tightened — only approved devices can talk to your OpenClaw instance.
Reaction authentication across all channels — emoji-based auth prevents fake messages triggering actions.
Thread-bound agents — one agent's context can't leak into another's.
Every one of these is enabled by default in recent versions.
Don't disable them to save time.
Rule #5 — Monitor Everything
The Lobster Board dashboard has system logs as a widget.
Put it front and centre.
Token tracker tells you if an agent is burning money.
Task board tells you what's running.
If something looks off — pause the session and investigate.
The course's advice: treat your agents like interns.
Trust but verify.
See my security monitoring dashboard 👉
The Molt Worker Deep Dive
This part of the course is underrated.
Molt Worker runs OpenClaw inside a Cloudflare worker.
Ephemeral.
Short-lived.
Tightly sandboxed.
When an agent task finishes — the environment dies.
State is saved externally.
Next run spawns fresh.
Benefits:
- Malicious skills can't persist
- No long-running processes to compromise
- Cloudflare's DDoS and WAF protection baked in
- Runs across the edge globally
For high-security or client work, Molt Worker is the answer.
OpenClaw Course Security-First Workflow
Here's the order the course teaches:
- Clone OpenClaw into a VM or Docker container.
- Set up external secrets management.
- Review every skill before installing.
- Enable all default security guards.
- Monitor Lobster Board logs daily.
- Rotate secrets monthly.
- Run sensitive workloads on Molt Worker.
Follow that and you dramatically reduce risk.
What Happens If You Don't
I've seen it.
Guy installs a sketchy skill.
Agent scrapes his .env file.
API keys leak.
Cloud bill hits £3,000 overnight.
Don't be that person.
The OpenClaw course gives you the playbook — just follow it.
OpenClaw Course Security Vs Speed Trade-Off
Yes, this adds friction.
Yes, you'll move slower the first week.
But by week two, the checks are muscle memory and you move faster than people running unsafe setups (because you're not rebuilding from an incident).
Security compounds.
Just like SEO.
Join AI Profit Lab for my full security toolkit 👉
Related Reads
FAQ
1. Is OpenClaw safe to run on my main laptop? Only if you sandbox it (VM or Docker) and audit every skill. Otherwise — no.
2. What's the fastest secure setup? Docker container with external secrets manager. 30 minutes to get going.
3. Do the default security guards slow OpenClaw down? Negligibly. You won't notice the overhead.
4. How often should I rotate secrets? Monthly at minimum. Weekly if you're handling client data.
5. Can I run OpenClaw on a shared machine? Only in an isolated container. Never on the bare host.
6. What's the single biggest security win? External secrets management. That one move stops most exfiltration attacks dead.